
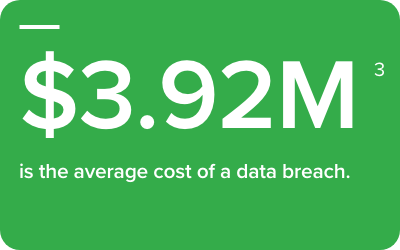
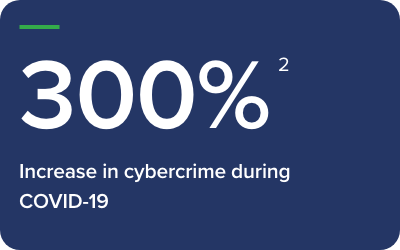
The threats posed by cybersecurity breaches and the demands they place on organizations have long been known, but they are in constant flux. Continuity is lost, infrastructure is proven obsolete, the brand’s reputation is put at stake and the budget is strained. As clear as the threats may be, current solutions can be confusing and ineffective if not properly designed or implemented. We learned from our practical field experience that many organizations are unaware of their true vulnerability until it is too late.
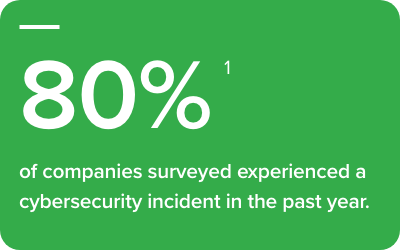


This rift cuts through an organization’s entire structure, and with a lack of appropriate procedures, unclear objectives, patchwork approaches and employee inexperience, these barriers have not only been laid bare, but enhanced—particularly in today’s times.

After listening carefully to our customers, and with our years of experience and industry expertise, we create dynamic environments that account for each individual circumstance. Much like the threats faced, effective solutions must run deep into an organization. There are four tenets to our approach: Education, Ownership, Technology and Policy.
The first and most important is Education. We inform, guide and train an organization’s teams at every level, particularly the C-suite. They receive the keys for preparedness, insight into present and future critical decisions, and a roadmap of the recovery process itself, which explains what gets recovered, the timeline and method. It is through education that our customers come to appreciate the depth of cyber-security and the potential need to rethink their existing infrastructure.
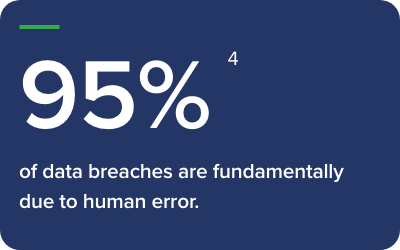

If education offers clarity, Ownership brings a change of perspective—beginning the transformation. While many companies today see security as a technological matter, it is inherently a business issue and should be considered a C-suite priority. When a company’s executives take responsibility and accountability, they are then in a position to implement those systems that address all aspects of their infrastructure and solutions.
To create a comprehensive framework which mitigates cybersecurity threats, Technology and Policy should work in tandem, security being part of all decisions. In terms of technology, Teknicor works with best-of-breed technologies like Palo Alto, Dell, VMware and Cisco. Supplementing the technological, a business’ policy and processes should be both proactive and reactive. The new framework should span multiple layers—insurance, legal and forensic—and must have all its elements tested from end-to-end.
Teknicor is a global provider of secure best-of-breed data centre infrastructure, data protection and managed cloud solutions. Our clients trust and rely on us to deliver fiscal responsibility, reduced risk, business continuity, lower complexity and increased agility. What we do is simple: we produce answers and deliver solutions. We are Innovation Unleashed.